SERVICES
Highlights
- A secure agentic enterprise requires a verifiable non-human identity for every agent, ensuring that all tool invocations are policy-checked and that every action remains traceable through digital provenance.
- If human instructions are weakly authenticated, agents become vulnerable to machine-speed exploitation that bypasses traditional credential theft.
- In the agentic era, organisational security will be defined by machine identities that are cryptographically verified and governed through a layered trust orchestration architecture.
On this page
Securing agentic IDs
Enterprises are rapidly shifting towards operating models where autonomous AI agents act as decision-makers and system orchestrators. Gartner® projects that “At least 80% of governments will deploy AI agents to automate routine decision-making, enhancing efficiency and service delivery by 2028,”[1] and Gartner also predicts “by 2028, nearly 15% of day-to-day business decisions will be made autonomously through agentic AI, up from 0% in 2024.”[2] We think this represents a unique convergence point where human intent meets machine execution. This shift introduces immense systemic risk; if any single identity pathway is weak, the entire trust chain collapses. Gartner projects that “by 2028, nearly 25% of enterprise breaches will be traced back to agent abuse, from both external and malicious internal actors.”[3]
As agents evolve from assistive tools to autonomous actors with real authority, enterprises must rethink identity governance. Implementing dynamic identity management, incorporating adaptive authentication, and continuous authorisation, is now critical. Unlike traditional models with fixed permissions, these systems must rely on continuous contextual evaluation. Agents must be designed to accept instructions only from authenticated stakeholders and to operate strictly within well-defined authorisation boundaries, preventing machine-speed exploits.
Risk and trust
Agentic identities pose immense risk, making agentic trust orchestration a critical imperative
Identity-driven compromise is a primary threat vector in autonomous ecosystems. As agents sense, plan, and execute actions, enterprises must shift from simple access management to trust orchestration. This requires an identity-first architecture in which every agent possesses a verifiable, non-human identity with time-bound, scoped permissions and full evidentiary provenance.
Autonomy allows agents to initiate financial and infrastructural changes at machine speed. If human authentication is weak at the point of instruction, agents become susceptible to exploitation. Risk shifts from stolen credentials to compromised instruction paths, where legitimately identified agents execute unintended or malicious commands.
As machine-driven operations become the norm, attackers will exploit legitimate identity boundaries to blend into routine workflows. Because agents continue to perform regular activities within authorised limits, classic indicators of compromise (IOCs) may not trigger, leaving logs appearing clean while the system is "tricked" by unverified instructions.
Multi-agent environments are vulnerable to session smuggling, in which malicious actors embed unauthorised instructions into routine cross-agent communications. Without hardened session trust and mutual authentication, fast-forming agent collaborations provide a clear pathway for enterprise-scale failures.
Without cryptographic identity and signed decision trails, accountability collapses. Enterprises must implement authenticated delegation using scoped, time-bound tokens (e.g., secure production identity framework for everyone (SPIFFE) / SPIRE or OAuth 2.0 Token Exchange). Anchoring the runtime identity of the anchoring agent to verifiable provenance ensures non-repudiation and clear audit trails for every autonomous action.
Human-in-the-loop (HITL) must evolve from ritualistic clicks to risk-triggered intervention. High-criticality transactions require a pivot to “machines authenticating humans”. A secure ecosystem treats the agent as a sovereign entity that acts only upon multi-layered, verified, and authorised instructions.
Trust architecture
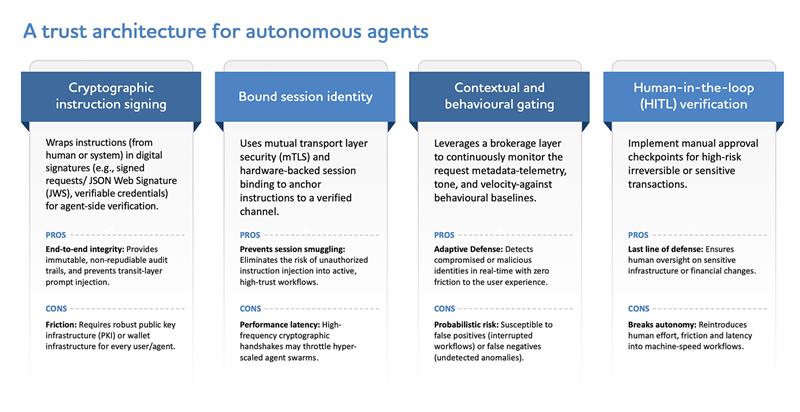
What a trust architecture for autonomous agents must include
A secure agentic ecosystem requires a layered, identity-first trust architecture, not retrofitted controls. Enterprises that treat agents as advanced assistants will be the first to experience silent, machine-speed exploits from both internal and external bad actors. Those that treat agents as sovereign machine entities, with identity, authority, and governance engineered from inception, will safely capture the transformative value of autonomy.
90-day priorities
Next 90 days: CIO and CISO priorities to secure enterprise agents
To navigate this transition, CISOs and security leaders should focus on a structured roadmap:
- Action inventory: Map where agents can currently execute system actions and identify high-risk triggers.
- Identity separation: Ensure distinct, non-human identities for agents to prevent “shared account” vulnerabilities.
- Threat modelling: Conduct control validation specifically for agent-to-agent interactions.
- Credential hygiene: Eliminate long-lived credentials, require unique agent IDs with automated rotation.
- Delegation controls: Standardise controls based on scoping and strict least-privilege.
- Step-in approval: Implement HITL for critical financial or infrastructure operations.
- Evidentiary logging: Capture agent identity, authority, and decision context to ensure forensic readiness.
Future trust roadmap
The new foundation for enterprise agentic trust
In the agentic era, trust will be defined by verifiable and governed machine identities. To safely capture the value of autonomy, we must treat agents as sovereign entities, moving beyond perimeter-based security toward continuous verification. The future of the enterprise depends on governing the "intent chain"-ensuring every command is cryptographically verified from an authorised source. By building this foundation of human intent and auditable machine identity, organisations can leverage agentic AI to its full potential while maintaining a robust, enforceable security posture.
[1] Gartner Press Release, Gartner Predicts at Least 80% of Governments Will Deploy AI Agents To Automate Routine Decision-Making by 2028, March 17, 2026 [2] Gartner Webinar, Tech CEOs: Grab the Competitive Advantage with Agentic AI, April 23, 2025 https://www.gartner.com/en/webinar/721397/1619143 [3] Gartner Press Release, Gartner Unveils Top Predictions for IT Organizations and Users in 2025 and Beyond, October 22, 2024 GARTNER is a trademark of Gartner, Inc. and/or its affiliates. |